It's not a matter of "if you'll be hacked" it's when! That's sad to say but unfortunately in this...
AI-Powered Cyber Attacks: Essential Security Measures for 2026
For years, cybersecurity advice focused on one main threat: human hackers manually trying to break into systems. In 2026, that threat has evolved — and it’s far more dangerous.
Hackers are now using artificial intelligence to automate attacks, impersonate real people, and bypass traditional security measures at a scale we’ve never seen before. This isn’t science fiction. It’s already happening, and small businesses are one of the primary targets.
If your security hasn’t been updated recently, attackers are likely already ahead.
What Are AI-Powered Cyber Attacks?
AI-powered cyberattacks use machine learning and automation tools to make hacking faster, smarter, and harder to detect. Instead of relying on one person manually crafting an attack, hackers now deploy AI systems that can:
-
Analyze thousands of email conversations
-
Mimic writing styles of executives and vendors
-
Generate highly convincing phishing emails in seconds
-
Automatically test passwords and login attempts
-
Adapt attacks based on security responses
In simple terms: hackers no longer need skill or time — AI does the work for them.
Why Small Businesses Are the Primary Target
Many business owners assume hackers focus on large corporations. In reality, small and mid-sized businesses are often easier targets — and more profitable.
Why?
-
Fewer security layers
-
Outdated antivirus software
-
Weak passwords and reused credentials
-
No active monitoring
-
Employees without cybersecurity training
AI tools allow attackers to scan thousands of businesses automatically and strike wherever defenses are weakest. That means size no longer offers protection.
The New Capabilities of AI Hackers
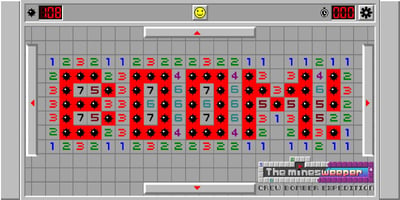
Here’s what modern AI-powered hackers can already do in 2026:
1. Generate Hyper-Realistic Phishing Emails
AI can study real email conversations and produce messages that look identical to a CEO, bookkeeper, or vendor. These emails often reference real projects, invoices, or conversations — making them extremely difficult to spot.
2. Impersonate Trusted Contacts
Attackers can clone tone, formatting, and writing style to impersonate executives, suppliers, or clients, requesting wire transfers, gift cards, or password resets.
3. Automate Attacks 24/7
AI systems don’t sleep. They test credentials, scan vulnerabilities, and launch attacks continuously — even on weekends and holidays.
4. Bypass Basic Security Tools
Traditional antivirus software alone is no longer enough. AI attacks can adapt in real time to avoid detection by outdated tools.
Why “Basic Antivirus” Is No Longer Enough
Many businesses still rely on the same security approach they used years ago:
-
Antivirus installed once
-
Rare updates
-
No monitoring
-
No visibility into threats
This approach is no longer effective.
AI-powered attacks are designed to slip past basic defenses. Once inside, attackers can move laterally through systems, access email accounts, steal data, or deploy ransomware — often without being detected for weeks or months.
What Businesses Need in 2026: Layered Security
Modern cybersecurity is no longer about one tool. It’s about layers of protection working together.
A proper 2026-ready security strategy includes:
Email Security
Advanced filtering to stop phishing and impersonation attempts before they reach employees.
Endpoint Protection
Modern antivirus combined with behavioral detection to identify suspicious activity.
Identity & Access Controls
Strong password policies, multi-factor authentication, and controlled user access.
Patch Management
Keeping systems updated so known vulnerabilities can’t be exploited.
24/7 Monitoring
Real-time alerts when something unusual happens — not weeks later.
Human Support
A professional IT team watching over your systems and responding immediately when threats appear.
This layered approach dramatically reduces the risk of AI-driven attacks.
The Cost of Falling Behind
Businesses that don’t update their security face real consequences:
-
Financial losses
-
Stolen client data
-
Downtime and lost productivity
-
Reputational damage
-
Potential legal and compliance issues
In many cases, recovery costs far exceed what proactive security would have cost in the first place.
How Fine Technologies Helps Protect Businesses in 2026
At Fine Technologies, we help small businesses stay ahead of modern cyber threats — without overwhelming them with technical jargon.
Our services include:
-
Advanced antivirus and endpoint protection
-
Password management and identity security
-
Patch management
-
24/7 system monitoring
-
Help desk support
-
Microsoft, Adobe, and Dell solutions
Most importantly, we take a proactive approach — identifying and stopping threats before they become disasters.
Final Thought: AI Hackers Aren’t Coming — They’re Already Here
Cybercrime has entered a new era. AI-powered hackers are faster, smarter, and more convincing than ever before.
The question is no longer if your business will be targeted — it’s whether your defenses are ready.
If your security hasn’t been reviewed recently, now is the time.
Fine Technologies
📞 813-702-9672
🌐 https://fine-technologies.com
Let us help make sure your business stays protected in 2026 — while you focus on running it.